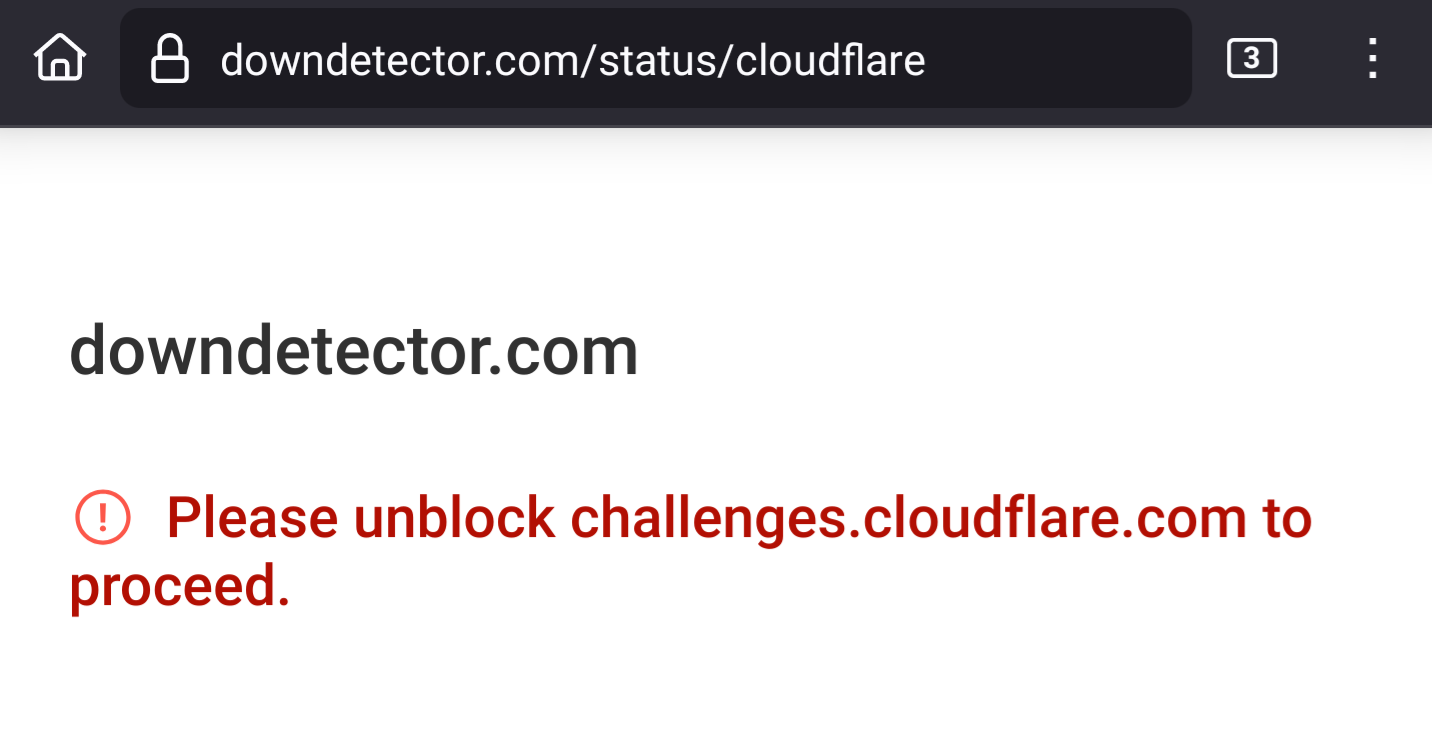
Downdetector wants to issue a cloudlfare challenge, but cannot because of the current cloudflare outage. Instead of letting me through or supplying a useful error message, this is what it says. As if I, and my ad blocker, are to blame.<br><br><br>Screenshot reads:<br><br>downdetector.com<br>Please unblock challenges.cloudflare.com to proceed.<br><br><a href="/tags/tech/" rel="tag">#tech</a> <a href="/tags/dev/" rel="tag">#dev</a> <a href="/tags/web/" rel="tag">#web</a> <a href="/tags/darkpatterns/" rel="tag">#DarkPatterns</a> <a href="/tags/downdetector/" rel="tag">#DownDetector</a> <a href="/tags/cloudflare/" rel="tag">#cloudflare</a> <a href="/tags/cloudflareoutage/" rel="tag">#CloudflareOutage</a> <a href="/tags/everythingisbroken/" rel="tag">#EverythingIsBroken</a><br>
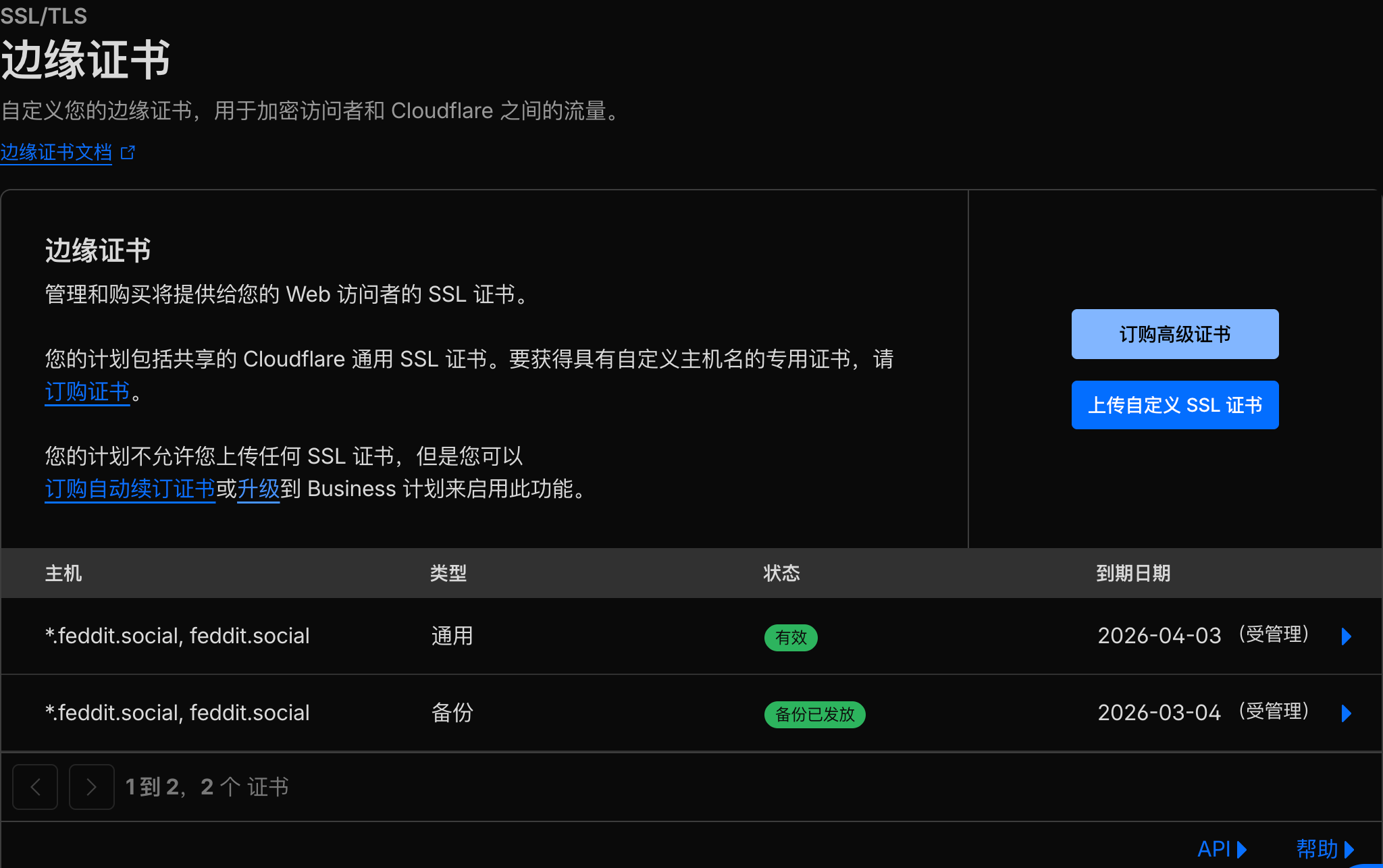
cloudflare
My website and fedi instance still works because it's not behind <a href="/tags/cloudflare/" rel="tag">#Cloudflare</a>. Just sayin'.<br><br><a href="/tags/selfhost/" rel="tag">#SelfHost</a><br>
<p>Hilariously, I found out about the <a href="/tags/cloudflare/" rel="tag">#Cloudflare</a> outage by trying to use a goat gestation calculator from the American Goat Society after breeding the first goat of the year this morning.</p>
<p>Today is my first day on Cloudflare!</p><p>Just had Claude clean up my code while I was vibe coding.</p><p>Committing it to main right now!</p><p>Happy to be part of the team</p><p><a href="/tags/programmerhumor/" rel="tag">#programmerhumor</a> <a href="/tags/cloudflare/" rel="tag">#cloudflare</a></p>
So <a href="/tags/cloudflare/" rel="tag">#Cloudflare</a> didn't have a unit test to catch the upper bound of func with an .unwrap(). It got through code review/linting/etc? A billion dollar company and responsible for a huge potion of traffic?<br><br>At what point do these failures become malpractice/negligence and subject to regulatory fines?<br>
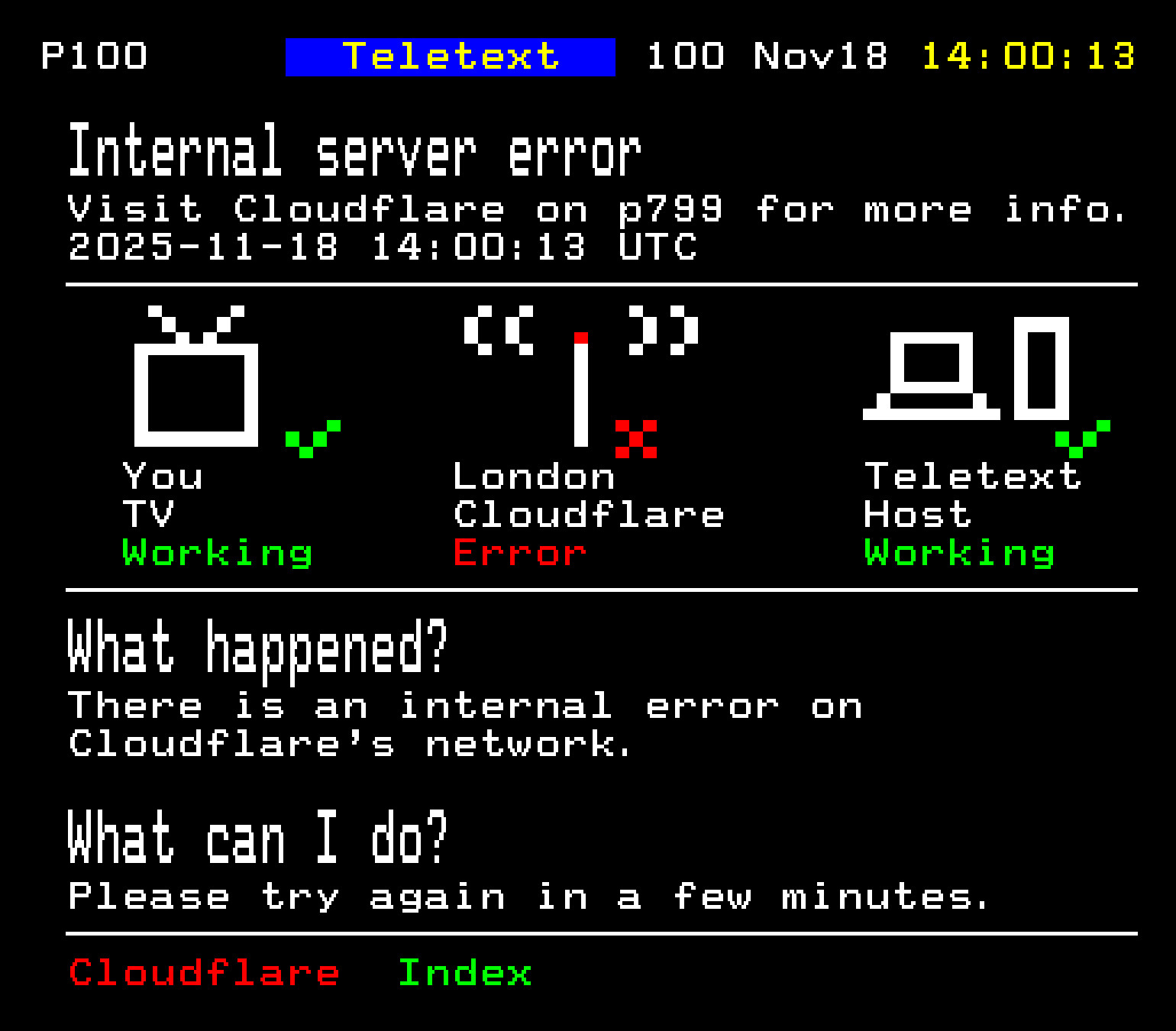
<p>A (horrible) alternate reality, inspired by yesterday.</p><p><a href="/tags/cloudflare/" rel="tag">#Cloudflare</a> <a href="/tags/teletext/" rel="tag">#Teletext</a> <a href="/tags/teletextart/" rel="tag">#TeletextArt</a> <a href="/tags/art/" rel="tag">#Art</a></p>
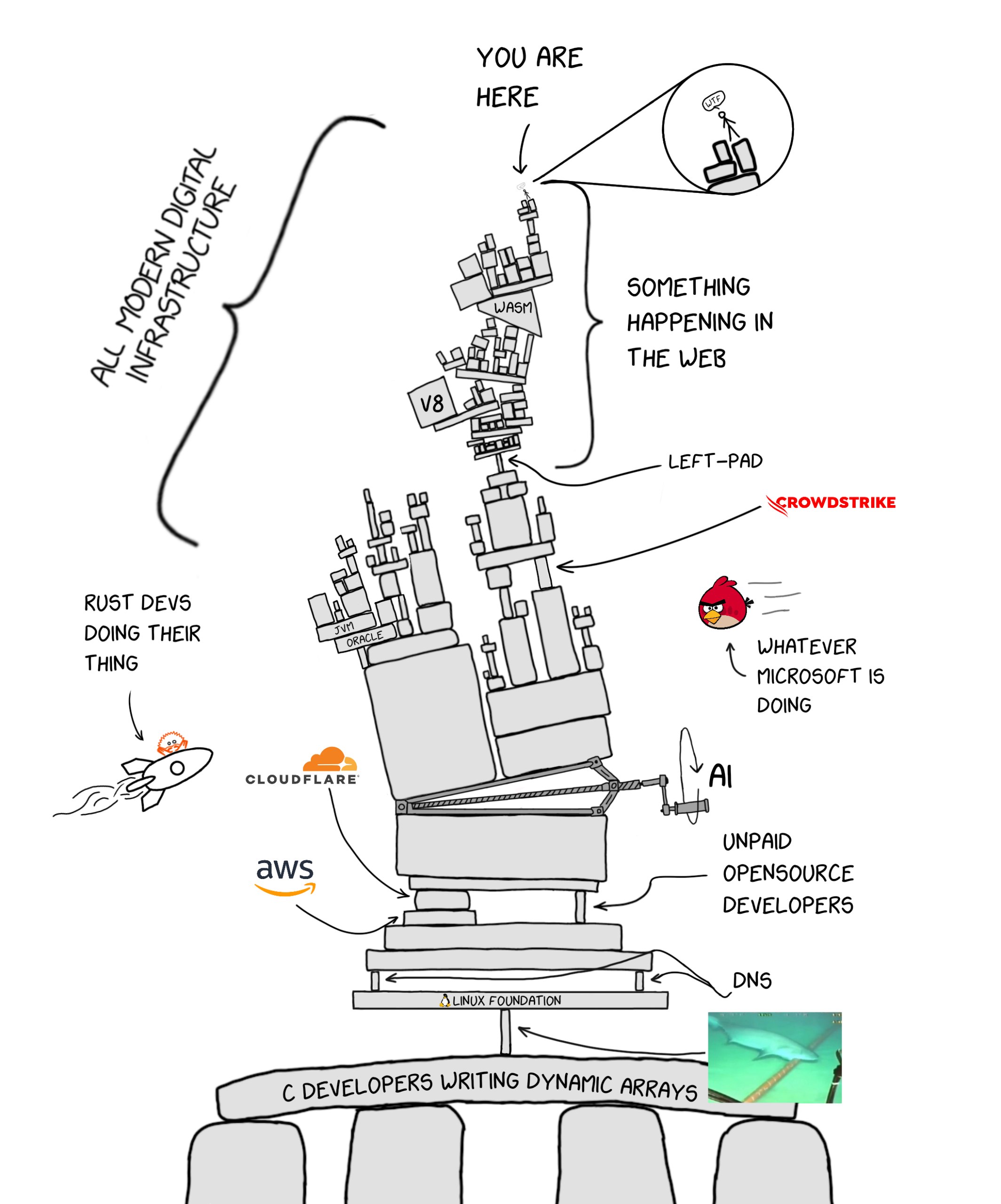
<a href="/tags/internet/" rel="tag">#internet</a> <a href="/tags/infrastructure/" rel="tag">#infrastructure</a> <a href="/tags/cloudflare/" rel="tag">#cloudflare</a> <a href="/tags/microsoft/" rel="tag">#microsoft</a> <a href="/tags/ai/" rel="tag">#AI</a> <a href="/tags/aws/" rel="tag">#aws</a> <a href="/tags/crowdstrike/" rel="tag">#crowdstrike</a> <a href="/tags/dns/" rel="tag">#DNS</a> <a href="/tags/rust/" rel="tag">#rust</a> <a href="/tags/linux/" rel="tag">#Linux</a>
Edited 136d ago
<p><a href="/tags/fedify/" rel="tag">#Fedify</a> 1.6 is approaching with three major enhancements: RFC 9421 HTTP Message Signatures support with double-knocking for seamless backward compatibility, a new builder pattern for better code organization in large applications, and native <a href="/tags/cloudflare/" rel="tag">#Cloudflare</a> <a href="/tags/workers/" rel="tag">#Workers</a> support for serverless deployments. These additions strengthen Fedify's standards compliance while expanding deployment flexibility across different environments. Stay tuned for the official release! 🚀</p><p><a href="/tags/activitypub/" rel="tag">#ActivityPub</a> <a href="/tags/fedidev/" rel="tag">#fedidev</a> <a href="/tags/fediverse/" rel="tag">#fediverse</a> <a href="/tags/rfc9421/" rel="tag">#RFC9421</a> <a href="/tags/cloudflareworkers/" rel="tag">#CloudflareWorkers</a></p>
<p>Valtteri Laitinen (<a href="https://fedi.valtlai.fi/@valtlai" rel="nofollow">@valtlai</a>) managed to get <a href="/tags/fedify/" rel="tag">#Fedify</a> running on <a href="/tags/cloudflare/" rel="tag">#Cloudflare</a> Workers!</p><p><a href="/tags/cloudflareworkers/" rel="tag">#CloudflareWorkers</a> <a href="/tags/fedidev/" rel="tag">#fedidev</a> <a href="/tags/activitypub/" rel="tag">#ActivityPub</a></p><p><a href="https://fedi.valtlai.fi/@valtlai/113906145660141267" rel="nofollow" class="ellipsis" title="fedi.valtlai.fi/@valtlai/113906145660141267"><span class="invisible">https://</span><span class="ellipsis">fedi.valtlai.fi/@valtlai/11390</span><span class="invisible">6145660141267</span></a></p>
If Cloudflare really is "verifying" that I'm human with its obnoxious widget, why does it do this for multiple web sites and over and over again for a given web site? Shouldn't it be able to verify I'm human once and for all? What exactly are they doing with their sprawling control of all these web sites if not adding value through economy of scale?<br><br><a href="/tags/cloudflare/" rel="tag">#Cloudflare</a> <a href="/tags/securitytheater/" rel="tag">#SecurityTheater</a> <a href="/tags/surveillance/" rel="tag">#surveillance</a> <a href="/tags/web/" rel="tag">#web</a> <a href="/tags/tech/" rel="tag">#tech</a> <a href="/tags/dev/" rel="tag">#dev</a> <a href="/tags/darkpattern/" rel="tag">#DarkPattern</a><br>
I just had to "prove" I am human to view a shop listing for a refrigerator.<br><br><a href="/tags/captcha/" rel="tag">#captcha</a> <a href="/tags/bot/" rel="tag">#bot</a> <a href="/tags/human/" rel="tag">#human</a> <a href="/tags/cloudflare/" rel="tag">#CloudFlare</a> <a href="/tags/web/" rel="tag">#web</a> <a href="/tags/tech/" rel="tag">#tech</a> <a href="/tags/dev/" rel="tag">#dev</a><br>
Once again a fully automated, non-human system is denying me access to a resource on the internet because it has determined I am not human enough.<br><br><a href="/tags/2025/" rel="tag">#2025</a> <a href="/tags/dystopia/" rel="tag">#dystopia</a> <a href="/tags/cloudflare/" rel="tag">#Cloudflare</a> <a href="/tags/ai/" rel="tag">#AI</a> <a href="/tags/human/" rel="tag">#human</a> <a href="/tags/web/" rel="tag">#web</a> <a href="/tags/tech/" rel="tag">#tech</a> <a href="/tags/dev/" rel="tag">#dev</a><br>
<p>在config.yaml内将远程媒体缓存默认配置从</p><p>media-remote-cache-days 7media-cleanup-from "00:00“media-cleanup-every "24h"</p><p>修改为</p><p>media-remote-cache-days 2media-cleanup-from "00:00“media-cleanup-every "8h"</p><p>目前在Cloudflare R2的存储空间为6.26GB<br>等过一段时间再看看<br>当然也可以通过GTS Cli手动执行清理<br>但是我运行在docker内,不启动gotosocial_main就无法执行docker exec -it gotosocial_main sh和./gotosocial admin media prune remote<br>但是这个命令必须在Gotosocial未运行时起作用。<br>求赐教</p><p>删除孤立媒体:<br>./gotosocial admin media prune orphaned</p><p><a href="/tags/cloudflare/" rel="tag">#cloudflare</a> <a href="/tags/r2/" rel="tag">#r2</a> <a href="/tags/s3/" rel="tag">#s3</a> <a href="/tags/object_storage/" rel="tag">#object_storage</a> <a href="/tags/cache/" rel="tag">#cache</a> <a href="/tags/gotosocial/" rel="tag">#gotosocial</a> <a href="/tags/cli/" rel="tag">#cli</a></p>
<p>Cloudflare 发现 Perplexity 的秘密爬虫会伪装 User-Agent 爬取其它网站,并且不遵守 robots.txt。<br><br>- Cloudflare 注册了一个新域名,配置了禁止任何爬虫的 robots.txt,在 Cloudflare 上禁止 GenAI 爬虫访问。<br>- 在询问 Perplexity 关于一个此域名下子域名的详细信息的时候,Perplexity 依然可以做出一些回答。<br>- Cloudflare 发现 Perplexity 以 macOS 上 Chrome 的 User-Agent 伪装自己,通过未宣告在文档所述自有 IP 段中的,来自多个 ASN 的 IP 访问了此域名。<br>- Cloudflare 通过机器学习等技术尝试识别并拦截此类爬取行为。测试发现当爬取被拦截时,Perplexity 转用了其它数据源,说明拦截确有起效。<br>- 文章还提到,OpenAI 旗下的 ChatGPT 会访问并遵守 robots.txt,尊重了网站主对爬虫的要求。<br>- Cloudflare Bot Management 用户现已可使用相关规则拦截 Perplexity 的秘密爬虫。<br><br><a href="https://blog.cloudflare.com/perplexity-is-using-stealth-undeclared-crawlers-to-evade-website-no-crawl-directives/" rel="nofollow">blog.cloudflare.com/~</a><br><br>[感谢 Pop 提供此消息。]<br><br><a href="/tags/genai/" rel="tag">#GenAI</a> <a href="/tags/cloudflare/" rel="tag">#Cloudflare</a> <a href="/tags/perplexity/" rel="tag">#Perplexity</a><br><br><a href="https://t.me/outvivid/4741" rel="nofollow">Telegram 原文</a></p>
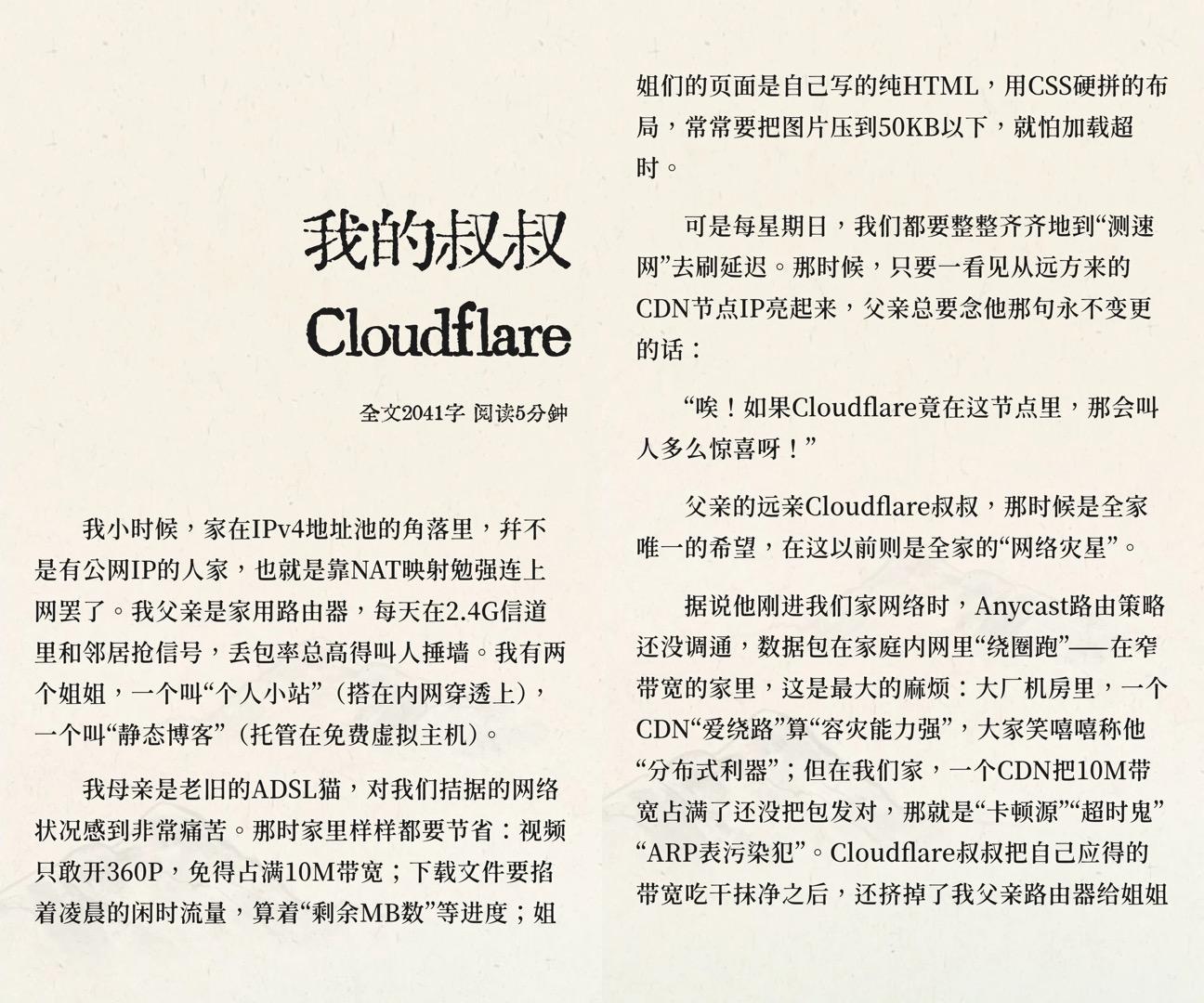
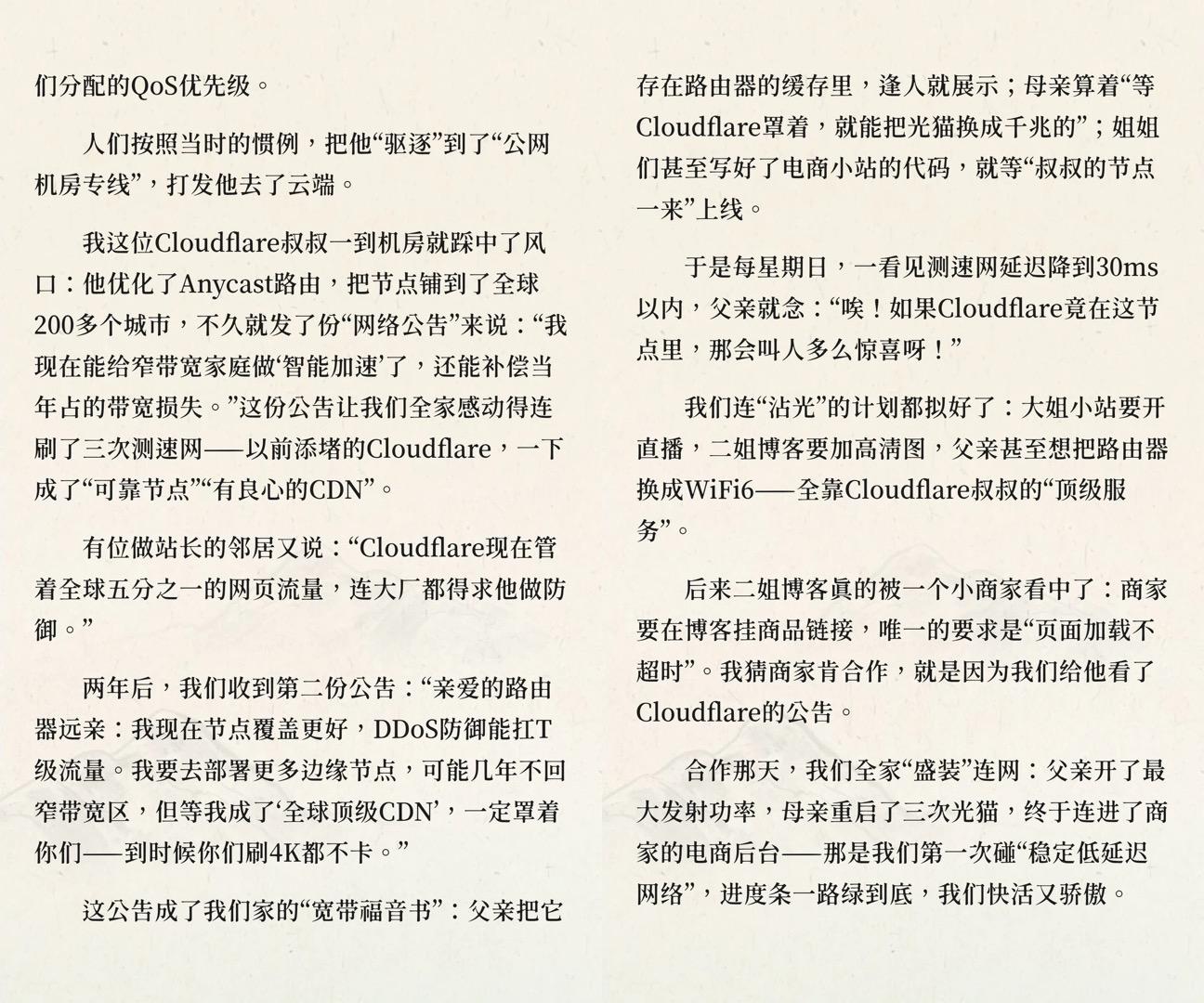
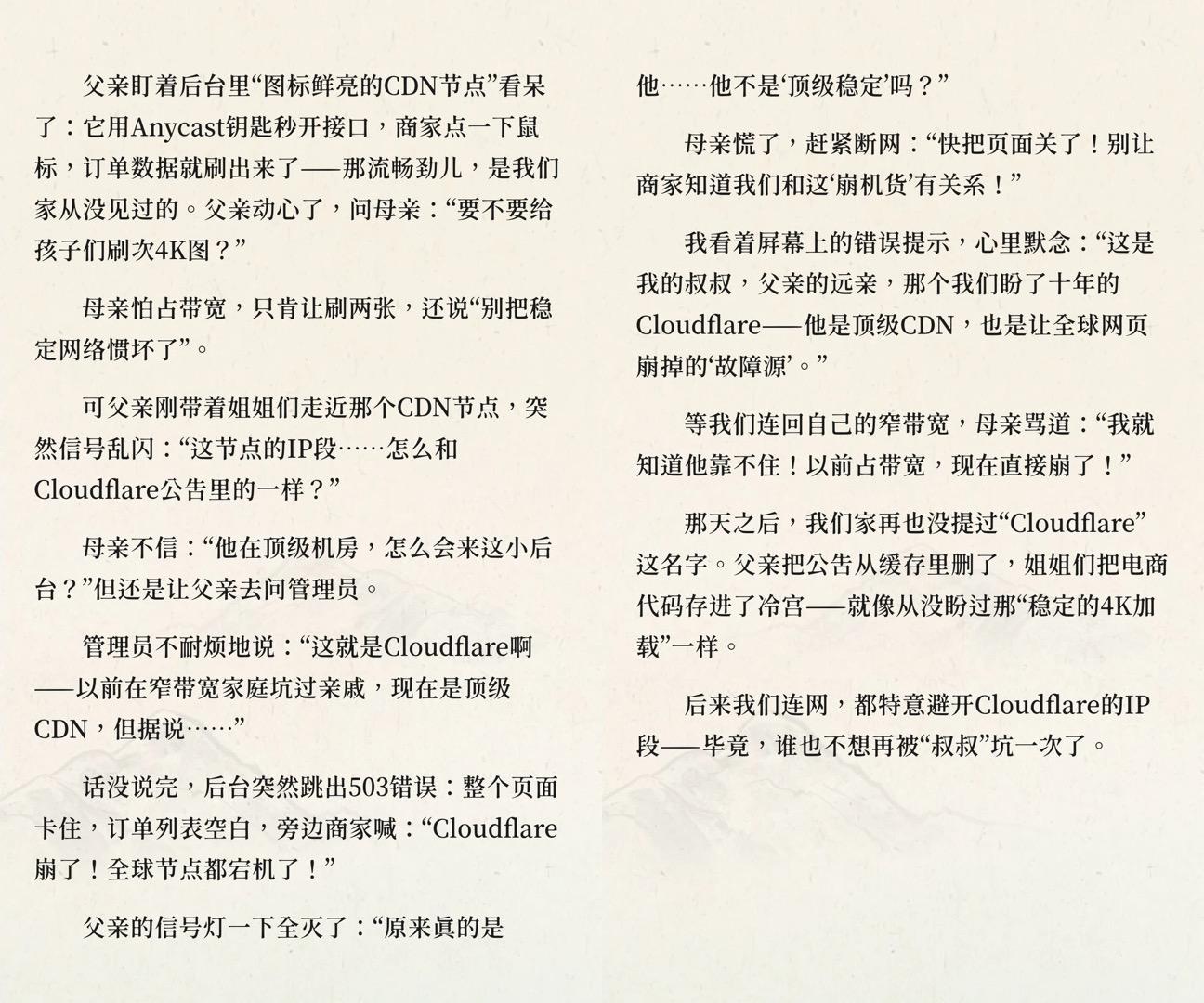
<p>《我的叔叔Cloudflare》</p><p>全文2041字,阅读5分钟<br>已通过拼接满足Mastodon要求的4张图片以下<br>图片来源于QQ</p><p><span class="h-card"><a href="https://ovo.st/club/board" class="u-url mention" rel="nofollow noopener noreferrer" target="_blank">@<span>board</span></a></span> <a href="/tags/cloudflare/" rel="tag">#cloudflare</a></p>
<p>Bueno, pues el post de ayer iba a ser un poco distinto, pero por aquello de lo del bloqueo de la puta liga en el que <span class="h-card"><a href="https://musician.social/@mirlo" class="u-url mention" rel="nofollow noopener noreferrer" target="_blank">@<span>mirlo</span></a></span> se ve afectado pues me ha salido hoy esto.</p><p>La noticia buena: ¡ya se pueden escuchar los temas en abierto!</p><p><a href="https://galeriaspreciados.band/all-your-base-are-belong-to-us/" rel="nofollow" class="ellipsis" title="galeriaspreciados.band/all-your-base-are-belong-to-us/"><span class="invisible">https://</span><span class="ellipsis">galeriaspreciados.band/all-you</span><span class="invisible">r-base-are-belong-to-us/</span></a></p><p><a href="/tags/indie/" rel="tag">#indie</a> <a href="/tags/diy/" rel="tag">#diy</a> <a href="/tags/musica/" rel="tag">#musica</a> <a href="/tags/cloudflare/" rel="tag">#cloudflare</a> <a href="/tags/laliga/" rel="tag">#laliga</a> <a href="/tags/fanzine/" rel="tag">#fanzine</a></p>
<p>Cloudflare 发现 Fina CA 一直在未经授权签发 <a href="http://1.1.1.1" rel="nofollow">1.1.1.1</a> 的 TLS 证书。<br><br>- Fina CA 是一家证书机关 (CA),其根证书目前在 Microsoft 的信任根证书库中。<br>- Cloudflare 人士最近从邮件列表获知此事件。<br>- 根据调查,自 2024 年二月起,Fina 就已签发了 12 个包含 IP 地址 <a href="http://1.1.1.1" rel="nofollow">1.1.1.1</a> 的证书;大多证书在签发后立即被 revoke。<br>- Cloudflare 在文档中提到其本来早就应该通过 Certificiate Transparency 监测获知此问题,但由于数个原因监测未能奏效。<br><br><a href="https://blog.cloudflare.com/unauthorized-issuance-of-certificates-for-1-1-1-1/" rel="nofollow">blog.cloudflare.com/~</a><br><br><a href="/tags/pki/" rel="tag">#PKI</a> <a href="/tags/cloudflare/" rel="tag">#Cloudflare</a> <a href="/tags/finaca/" rel="tag">#FinaCA</a><br><br><a href="https://t.me/outvivid/4748" rel="nofollow">Telegram 原文</a></p>
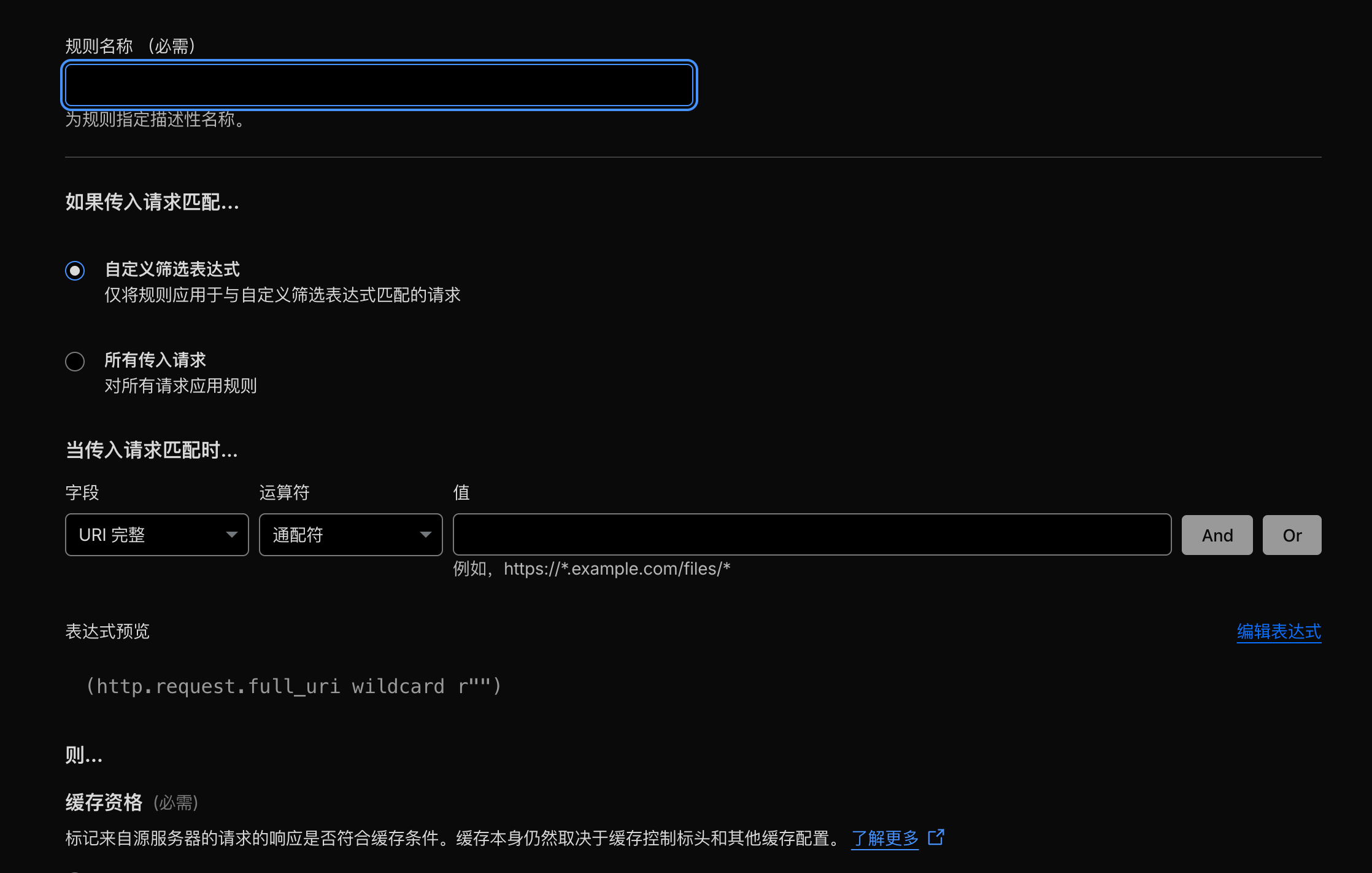
<p>开启这个插件竟然会让我无法编辑/选择Cloudflare某些部件,气煞我也<br> <br><a href="/tags/supercopy/" rel="tag">#SuperCopy</a> <a href="/tags/bug/" rel="tag">#bug</a> <a href="/tags/cloudflare/" rel="tag">#Cloudflare</a></p>
<p>I turned a tiny <a href="/tags/mac/" rel="tag">#Mac</a> mini into my own <a href="/tags/mastodon/" rel="tag">#Mastodon</a> server—secure, low‑maintenance, and running like a dream. Here’s the full build, from <a href="/tags/docker/" rel="tag">#Docker</a> to <a href="/tags/cloudflare/" rel="tag">#Cloudflare</a> Tunnel, and why <a href="/tags/selfhosting/" rel="tag">#SelfHosting</a> doesn’t have to be a headache.</p><p><a href="/tags/fediverse/" rel="tag">#Fediverse</a> <a href="/tags/activitypub/" rel="tag">#ActivityPub</a> <a href="/tags/homelab/" rel="tag">#HomeLab</a> <a href="/tags/devops/" rel="tag">#DevOps</a> <a href="/tags/sysadmin/" rel="tag">#SysAdmin</a></p><p><a href="https://phoenixtrap.com/2025/09/21/my-mini-mastodon-server/?utm_source=mastodon&utm_medium=jetpack_social" rel="nofollow" class="ellipsis" title="phoenixtrap.com/2025/09/21/my-mini-mastodon-server/?utm_source=mastodon&utm_medium=jetpack_social"><span class="invisible">https://</span><span class="ellipsis">phoenixtrap.com/2025/09/21/my-</span><span class="invisible">mini-mastodon-server/?utm_source=mastodon&utm_medium=jetpack_social</span></a></p>
<p>第一次收到这个邮件<br>发件人是:Cloudflare <[email protected]><br>Gemini解释:由于 CA/B 论坛的新规,某些情况下通配符证书不再支持 HTTP 验证,必须通过 DNS TXT 记录来证明你对该子域名的所有权。<br>Cloudflare Tunnel添加子域名时,会为该特定主机名申请一张“专用证书”。这种专用证书的优先级高于通配符证书。</p><p><a href="/tags/cloudflare/" rel="tag">#cloudflare</a> <a href="/tags/tunnel/" rel="tag">#tunnel</a> <a href="/tags/ssl/" rel="tag">#ssl</a> <a href="/tags/dns/" rel="tag">#dns</a> <a href="/tags/txt/" rel="tag">#txt</a></p>
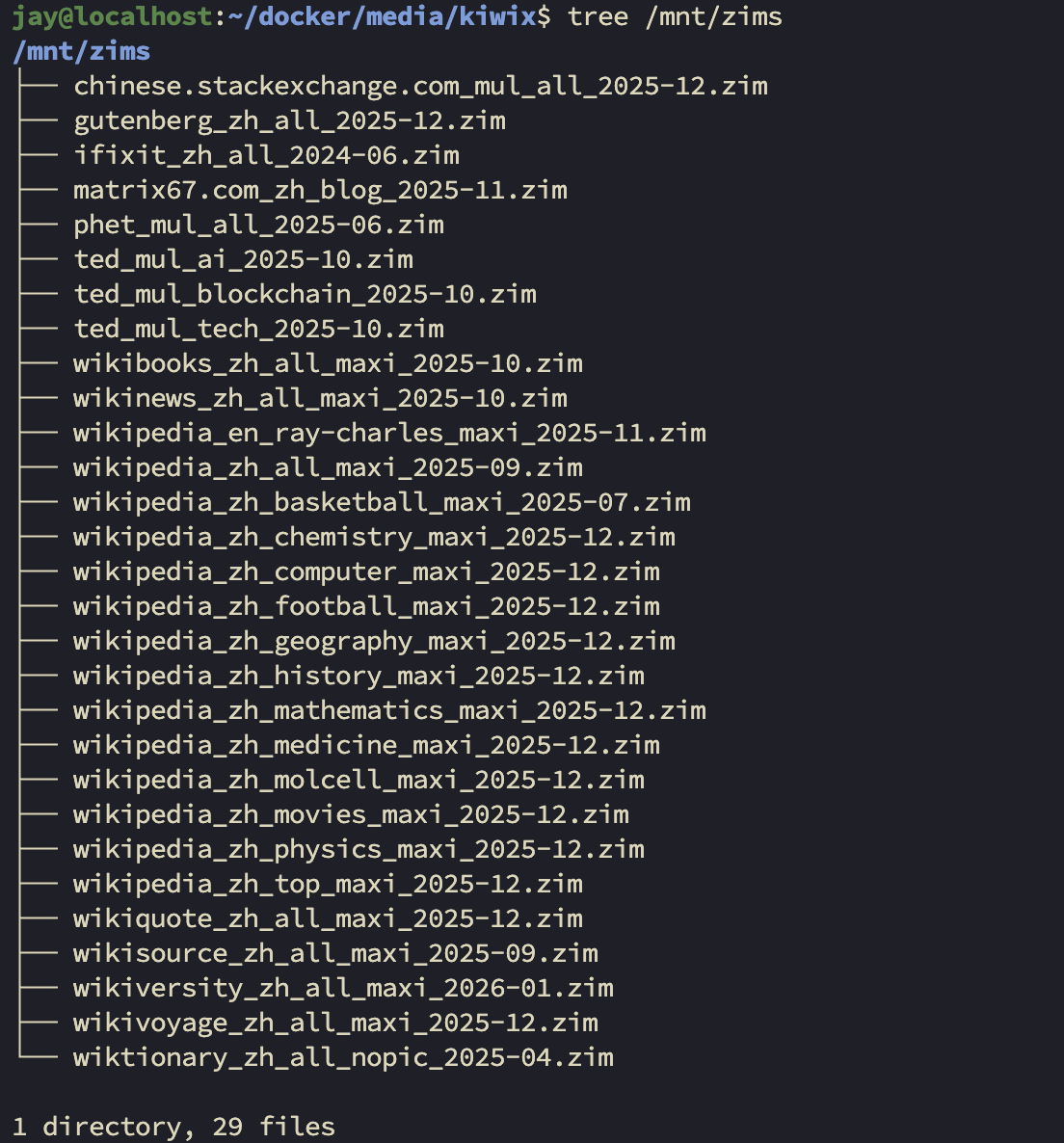
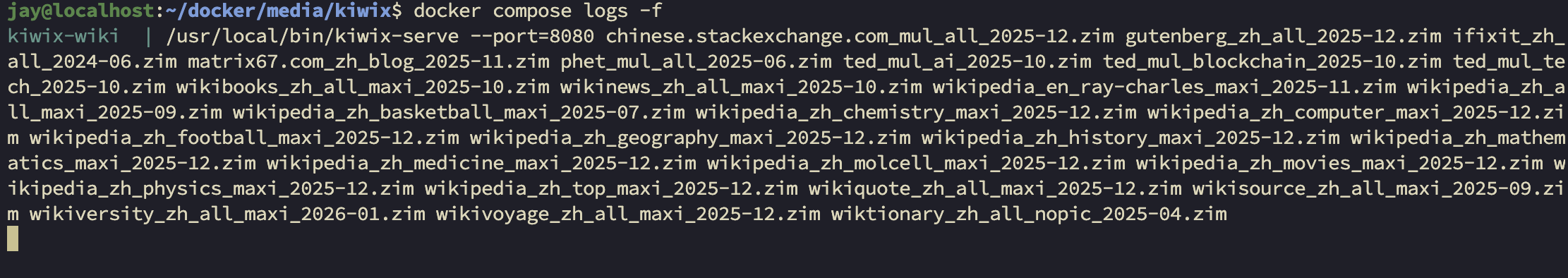
<p>RE: <a href="https://mstdn.feddit.social/@admin/115897274903877210" rel="nofollow" class="ellipsis" title="mstdn.feddit.social/@admin/115897274903877210"><span class="invisible">https://</span><span class="ellipsis">mstdn.feddit.social/@admin/115</span><span class="invisible">897274903877210</span></a></p><p>Rclone Mount再在Cloudflare CNAME+Rules,确实是免去了backblaze的流量费,但是这个kiwix的启动速度感觉比直接从backblaze拉慢了100倍...</p><p>感觉需要在Hetzner换一个新机器2X4TB HDD专门做镜像网站...<br>Kiwix-serve、Immich......</p><p><a href="/tags/rclone/" rel="tag">#rclone</a> <a href="/tags/cloudflare/" rel="tag">#cloudflare</a> <a href="/tags/backblaze/" rel="tag">#backblaze</a> <a href="/tags/bandwidth/" rel="tag">#Bandwidth</a> <a href="/tags/alliance/" rel="tag">#Alliance</a> <a href="/tags/hetzner/" rel="tag">#hetzner</a> <a href="/tags/kiwix/" rel="tag">#kiwix</a></p>








![[需要采取行动] 验证 navidrome.feddit.social 以续订 SSL 证书 [需要采取行动] 验证 navidrome.feddit.social 以续订 SSL 证书](/proxy/post_attachment/207785/c01af63d1a.png)