The 2025 Go Cryptography State of the Union by <span class="h-card"><a href="https://abyssdomain.expert/@filippo" class="u-url mention" rel="nofollow noopener noreferrer" target="_blank">@<span>filippo</span></a></span><br><br><a href="https://words.filippo.io/2025-state/" rel="nofollow"><span class="invisible">https://</span>words.filippo.io/2025-state/</a><br><br><a href="/tags/golang/" rel="tag">#GoLang</a> <a href="/tags/cryptography/" rel="tag">#Cryptography</a><br>
cryptography
You can now do Shamir's secret sharing in Hare and use it as a module or just install the CLI.<br><br><a href="https://git.sr.ht/~blainsmith/hare-shamir-secret-sharing" rel="nofollow" class="ellipsis" title="git.sr.ht/~blainsmith/hare-shamir-secret-sharing"><span class="invisible">https://</span><span class="ellipsis">git.sr.ht/~blainsmith/hare-sha</span><span class="invisible">mir-secret-sharing</span></a><br><br>Disclaimer: This has not been formerly audited so use at your own risk.<br><br><a href="/tags/cryptography/" rel="tag">#Cryptography</a> <a href="/tags/secretsharing/" rel="tag">#SecretSharing</a> <a href="/tags/harelang/" rel="tag">#HareLang</a><br>
I submitted a Pull Request to update MacPorts' OpenSSH to 9.9p2 here:<br><br><a href="https://github.com/macports/macports-ports/pull/27712" rel="nofollow" class="ellipsis" title="github.com/macports/macports-ports/pull/27712"><span class="invisible">https://</span><span class="ellipsis">github.com/macports/macports-p</span><span class="invisible">orts/pull/27712</span></a><br><br>GitHub Continuous Integration checks are running. Hopefully they will be OK (Update 2 out of 3 have completed successfully, which is a good sign).<br><br>I tested locally without issues, but I also build against LibreSSL locally, whereas GitHub CI and MacPorts' Build Bots I think default to OpenSSL.<br><br>This release is to address some vulnerabilities identified by Qualys and other less critical bugs.<br><br>More details from upstream here:<br><br><a href="https://www.openssh.com/releasenotes.html#9.9p2" rel="nofollow" class="ellipsis" title="www.openssh.com/releasenotes.html#9.9p2"><span class="invisible">https://</span><span class="ellipsis">www.openssh.com/releasenotes.h</span><span class="invisible">tml#9.9p2</span></a><br><br>Of particular note:<br><br>" Fix CVE-2025-26465 - ssh(1) in OpenSSH versions 6.8p1 to 9.9p1<br>(inclusive) contained a logic error that allowed an on-path<br>attacker (a.k.a MITM) to impersonate any server when the<br>VerifyHostKeyDNS option is enabled. This option is off by default.<br><br>* Fix CVE-2025-26466 - sshd(8) in OpenSSH versions 9.5p1 to 9.9p1<br>(inclusive) is vulnerable to a memory/CPU denial-of-service related<br>to the handling of SSH2MSGPING packets. This condition may be<br>mitigated using the existing PerSourcePenalties feature.<br><br>Both vulnerabilities were discovered and demonstrated to be exploitable<br>by the Qualys Security Advisory team. We thank them for their detailed<br>review of OpenSSH."<br><br>If I read everything correctly, these vulnerabilities primarily only impact the Portable OpenSSH releases (which is what MacPorts uses). However, OpenBSD has also issued the following errata to mitigate one of the issues as it also appears to impact OpenBSD users:<br><br>"008: SECURITY FIX: February 18, 2025 All architectures<br>sshd(8) denial of service relating to SSH2MSGPING handling. ssh(1) server impersonation when VerifyHostKeyDNS enabled.<br>A source code patch exists which remedies this problem."<br><br>Source code patch for OpenBSD here:<br><br><a href="https://ftp.openbsd.org/pub/OpenBSD/patches/7.6/common/008_ssh.patch.sig" rel="nofollow" class="ellipsis" title="ftp.openbsd.org/pub/OpenBSD/patches/7.6/common/008_ssh.patch.sig"><span class="invisible">https://</span><span class="ellipsis">ftp.openbsd.org/pub/OpenBSD/pa</span><span class="invisible">tches/7.6/common/008_ssh.patch.sig</span></a><br><br>Having written as much, it appears as if the main OpenSSH version for OpenBSD is still 9.9, so I am not going to make a submission for undeadly.org Other editors reading this are welcome to though, I just kind of have a lot of other stuff on my plate at present.<br><br>As usual, I also have too much going on in my life to want more responsibilities such as commit access within MacPorts, so it's up to someone else to merge it.<br><br>Update <a href="/tags/2/" rel="tag">#2</a>: I also decided to be a good Samaritan and reported the issue to Apple. Not that they have ever acknowledged my efforts for such things nor paid me from their bug bounty program in years of doing similar things. Because, OFC, Apple can't spare a penny to anyone like me. Maybe Qualys already reported it to them anyway (though they would have no obligation to do so, they did find the vulns and reported them upstream as would be expected).<br><br><a href="/tags/openssh/" rel="tag">#OpenSSH</a> <a href="/tags/macports/" rel="tag">#MacPorts</a> <a href="/tags/secureshell/" rel="tag">#SecureShell</a> <a href="/tags/infosec/" rel="tag">#InfoSec</a> <a href="/tags/cryptography/" rel="tag">#Cryptography</a> <a href="/tags/security/" rel="tag">#Security</a> <a href="/tags/cve/" rel="tag">#CVE</a> <a href="/tags/patchtuesday/" rel="tag">#PatchTuesday</a> <a href="/tags/opensource/" rel="tag">#OpenSource</a> <a href="/tags/openbsd/" rel="tag">#OpenBSD</a> <a href="/tags/macos/" rel="tag">#macOS</a><br>
Edited 1y ago
<p>Great, informative writeup of Cryptographic Gotchas: <a href="https://gotchas.salusa.dev/" rel="nofollow"><span class="invisible">https://</span>gotchas.salusa.dev/</a></p><p>Lots of fantastic references and links in there, too.</p><p><a href="/tags/cryptography/" rel="tag">#cryptography</a> <a href="/tags/crypto/" rel="tag">#crypto</a> <a href="/tags/security/" rel="tag">#security</a> <a href="/tags/infosec/" rel="tag">#infosec</a></p>
Wherein, LaurieWired attempts to explain concepts such as lattice cryptography to the masses:<br><br><a href="https://hypertextgarden.com/p/the-strongest-encryption-is-just" rel="nofollow" class="ellipsis" title="hypertextgarden.com/p/the-strongest-encryption-is-just"><span class="invisible">https://</span><span class="ellipsis">hypertextgarden.com/p/the-stro</span><span class="invisible">ngest-encryption-is-just</span></a><br><br><a href="/tags/lauriewired/" rel="tag">#LaurieWired</a> <a href="/tags/cryptography/" rel="tag">#Cryptography</a> <a href="/tags/lwe/" rel="tag">#LWE</a> <a href="/tags/learningwitherrors/" rel="tag">#LearningWithErrors</a> <a href="/tags/quantumresistant/" rel="tag">#QuantumResistant</a><br>
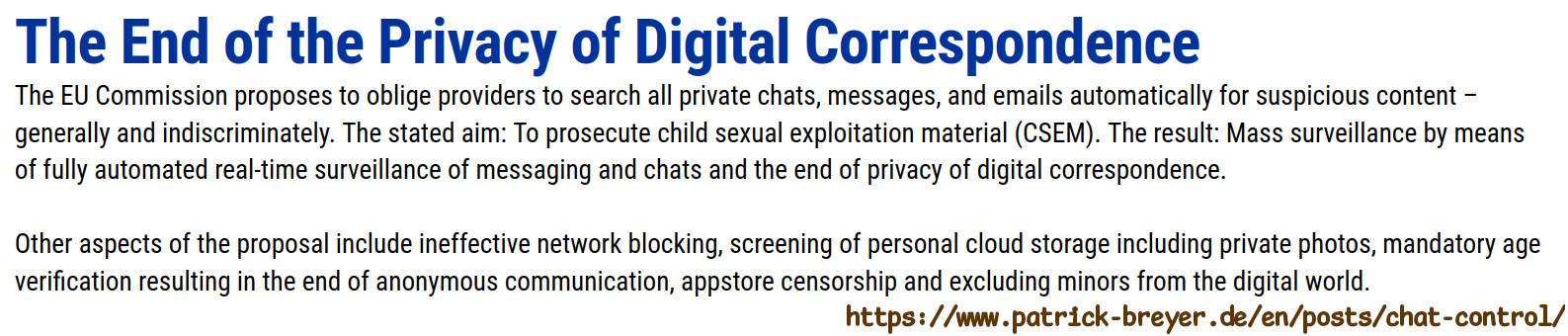
<p>The war on crypto never ends. The war on privacy, civil rights, security and freedom of speech never ends.</p><p>This time we are dangerously close to lose. The "Child Sexual Abuse" (CSA) EU regulation proposal, more aptly nicknamed "ChatControl", will be voted AGAIN this October, and many countries who opposed it last year are now undecided. The proposal at its roots aims at allowing authorities to break end-to-end encryption for the usual reason: "because of the children". As a father of two, I am disgusted by this recurring, cheap rhetoric.</p><p>What you can do: <a href="https://www.patrick-breyer.de/en/posts/chat-control/#WhatYouCanDo" rel="nofollow" class="ellipsis" title="www.patrick-breyer.de/en/posts/chat-control/#WhatYouCanDo"><span class="invisible">https://</span><span class="ellipsis">www.patrick-breyer.de/en/posts</span><span class="invisible">/chat-control/#WhatYouCanDo</span></a></p><p><a href="/tags/eu/" rel="tag">#eu</a> <a href="/tags/csa/" rel="tag">#CSA</a> <a href="/tags/csam/" rel="tag">#CSAM</a> <a href="/tags/chatcontrol/" rel="tag">#ChatControl</a> <a href="/tags/privacy/" rel="tag">#privacy</a> <a href="/tags/security/" rel="tag">#security</a> <a href="/tags/surveillance/" rel="tag">#surveillance</a> <a href="/tags/authoritarianism/" rel="tag">#authoritarianism</a> <a href="/tags/crypto/" rel="tag">#crypto</a> <a href="/tags/cryptography/" rel="tag">#cryptography</a> <a href="/tags/civilrights/" rel="tag">#civilrights</a></p>
<p>HBD, Martin Hellman! Hellman received the <a href="/tags/acmturingaward/" rel="tag">#ACMTuringAward</a> in 2015 for inventing and promulgating both asymmetric public-key <a href="/tags/cryptography/" rel="tag">#cryptography</a> and a practical cryptographic key-exchange method. Watch him explain the idea behind his Ph.D. dissertation: <a href="https://www.youtube.com/watch?v=umVSICLdrhM&t=2s" rel="nofollow" class="ellipsis" title="www.youtube.com/watch?v=umVSICLdrhM&t=2s"><span class="invisible">https://</span><span class="ellipsis">www.youtube.com/watch?v=umVSIC</span><span class="invisible">LdrhM&t=2s</span></a></p>
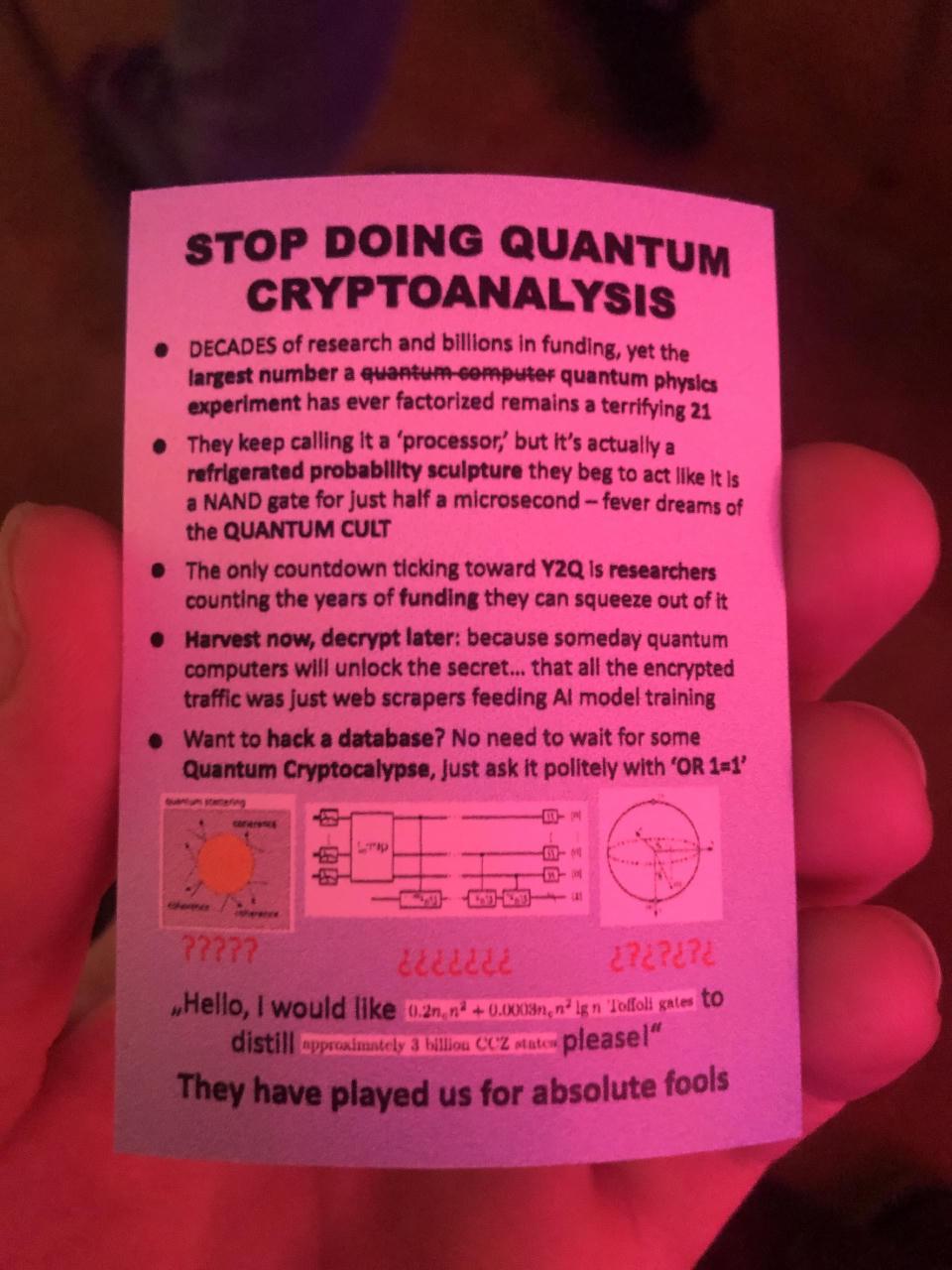
<p>From somewhere at <a href="/tags/39c3/" rel="tag">#39c3</a></p><p><a href="/tags/quantum/" rel="tag">#quantum</a> <a href="/tags/cryptography/" rel="tag">#cryptography</a> <a href="/tags/security/" rel="tag">#security</a></p>
I submitted a Pull Request to update MacPorts' signify to 1.62 here:<br><br><a href="https://github.com/macports/macports-ports/pull/31080" rel="nofollow" class="ellipsis" title="github.com/macports/macports-ports/pull/31080"><span class="invisible">https://</span><span class="ellipsis">github.com/macports/macports-p</span><span class="invisible">orts/pull/31080</span></a><br><br>GitHub Continuous Integration checks queued.<br><br>Hopefully they will run without issue?<br><br>If so, it's up to someone else with commit access to merge it.<br><br>This isn't very significant from the last PR I submitted from late October 2025 (upstream has a commit from early September 2025 so I am trailing by many months with this one) however, remarkable to me:<br><br>MacPorts' signify's version is now in alignment with upstream's versioning!<br><br>Yay!<br><br>I have no idea if that was true previously? My guess is: no, since I think jpouellet/Jean-Philippe Ouellet branched that out a long time ago and seemed to have iterated version tags haphazardly? Maybe I am mistaken though! There's a completely different Linuxism fork of signify which seems to have evolved (and versioned) very differently too.<br><br>That in particular has confused me with spurious repology.org out of date error messages for many months. I dunno if it has confused others, or if this version sync will make things less confusing, but hopefully? It makes things less confusing for me at least.<br><br>In tangential news, since I saw tedu in the man page, someone was wondering where he got off to a while ago and I don't think I saw a response. Hopefully he's doin OK? Please?<br><br><a href="/tags/signify/" rel="tag">#signify</a> <a href="/tags/macports/" rel="tag">#MacPorts</a> <a href="/tags/macos/" rel="tag">#macOS</a> <a href="/tags/opensource/" rel="tag">#OpenSource</a> <a href="/tags/openbsd/" rel="tag">#OpenBSD</a> <a href="/tags/cryptography/" rel="tag">#cryptography</a><br>
<p>We are excited to share our latest work on making secure messaging more decentralized!</p><p>We've developed DMLS – a new approach that brings fork resilience to the MLS protocol, solving a key challenge in distributed systems while maintaining Forward Secrecy.</p><p>This work was made possible by eQualitie, who funded it as part of the SplinterCon Breakout program.</p><p><a href="/tags/cryptography/" rel="tag">#Cryptography</a> <a href="/tags/messaginglayersecurity/" rel="tag">#MessagingLayerSecurity</a> <a href="/tags/decentralizedmessaging/" rel="tag">#DecentralizedMessaging</a> <a href="/tags/messaging/" rel="tag">#Messaging</a> <a href="/tags/opensource/" rel="tag">#OpenSource</a> <a href="/tags/security/" rel="tag">#Security</a> <a href="/tags/e2ee/" rel="tag">#E2EE</a> <a href="/tags/encryption/" rel="tag">#Encryption</a></p><p><a href="https://blog.phnx.im/making-mls-more-decentralized/" rel="nofollow" class="ellipsis" title="blog.phnx.im/making-mls-more-decentralized/"><span class="invisible">https://</span><span class="ellipsis">blog.phnx.im/making-mls-more-d</span><span class="invisible">ecentralized/</span></a></p>
<p>1/</p><p>One way ActivityPub can be extended is — through JSON-LD namespaces.</p><p>For example, many Fediverse servers use the following JSON-LD namespace to specify cryptographic public-key(s) for the user.</p><p><a href="https://w3id.org/security/v1" rel="nofollow"><span class="invisible">https://</span>w3id.org/security/v1</a></p><p>(This particular namespace is an HTTPS URL.)</p><p>...</p><p>But, does extant Fediverse software support cryptographic public-key(s) well?</p><p>...</p><p><a href="/tags/activitypub/" rel="tag">#ActivityPub</a> <a href="/tags/cryptography/" rel="tag">#Cryptography</a> <a href="/tags/fedidev/" rel="tag">#Fedidev</a> <a href="/tags/fedidevs/" rel="tag">#Fedidevs</a> <a href="/tags/fediverse/" rel="tag">#Fediverse</a> <a href="/tags/jsonld/" rel="tag">#JSONLD</a></p>