<p>RE: <a href="https://hachyderm.io/@evacide/115900663566563599" rel="nofollow" class="ellipsis" title="hachyderm.io/@evacide/115900663566563599"><span class="invisible">https://</span><span class="ellipsis">hachyderm.io/@evacide/11590066</span><span class="invisible">3566563599</span></a></p><p>Vulnerability introduced by AI-enhanced media processing.</p><p>• Attackers can leverage tiny memory corruption windows<br>• Media decoder memory layouts present consistent security vulnerabilities</p><p>thank you 🙇🏻 <span class="h-card"><a href="https://hachyderm.io/@evacide" class="u-url mention" rel="nofollow noopener noreferrer" target="_blank">@<span>evacide</span></a></span> for this high-quality explainer with references:</p><p>1. CVE-2025-49415<br>2. CVE-2025-54957<br>3. CVE-2025-36934<br>4. Dolby Digital (DD) and Dolby Digital Plus (DD+) audio formats<br>5. ETSI audio format specification</p><p>this isn't over imo. <a href="/tags/infosec/" rel="tag">#infosec</a></p>
infosec
<p>New blogpost: AI will compromise your cybersecurity posture<br><a href="https://rys.io/en/181.html" rel="nofollow"><span class="invisible">https://</span>rys.io/en/181.html</a></p><p>The way “AI” is going to compromise your cybersecurity is not through some magical autonomous exploitation by a singularity from the outside, but by being the poorly engineered, shoddily integrated, exploitable weak point you would not have otherwise had on the inside.</p><p>LLM-based systems are insanely complex. And complexity has real cost and introduces very real risk.</p><p>1/🧵</p><p><a href="/tags/ai/" rel="tag">#AI</a> <a href="/tags/infosec/" rel="tag">#InfoSec</a></p>
A web site just blocked me because I solved one of those sliding jigsaw puzzle captchas too quickly.<br><br><a href="/tags/tech/" rel="tag">#tech</a> <a href="/tags/dev/" rel="tag">#dev</a> <a href="/tags/web/" rel="tag">#web</a> <a href="/tags/captcha/" rel="tag">#captcha</a> <a href="/tags/cybersecurity/" rel="tag">#cybersecurity</a> <a href="/tags/infosec/" rel="tag">#infosec</a> <a href="/tags/securitytheater/" rel="tag">#SecurityTheater</a> <a href="/tags/darkpatterns/" rel="tag">#DarkPatterns</a><br>
<p>Overwhelmed by randomness of my toots? Protip: you don't need to follow me/people, you can just follow hashtags for interaction. I use several, like: <br><a href="/tags/infosec/" rel="tag">#InfoSec</a> <a href="/tags/privacy/" rel="tag">#Privacy</a> <a href="/tags/venice/" rel="tag">#Venice</a> <a href="/tags/food/" rel="tag">#Food</a> <a href="/tags/art/" rel="tag">#Art</a> <a href="/tags/f1/" rel="tag">#F1</a> <a href="/tags/caturday/" rel="tag">#Caturday</a> (yup) & <a href="/tags/lazypip/" rel="tag">#LazyPip</a> <a href="/tags/education/" rel="tag">#Education</a> <a href="/tags/security/" rel="tag">#Security</a> <a href="/tags/photography/" rel="tag">#Photography</a> <a href="/tags/motorbike/" rel="tag">#Motorbike</a> & <a href="/tags/ducati/" rel="tag">#Ducati</a> <a href="/tags/thenetherlands/" rel="tag">#theNetherlands</a> <a href="/tags/photochallenge/" rel="tag">#PhotoChallenge</a></p>
<p>New, from me: The Kimwolf Botnet is Lurking in Corporate, Govt. Networks</p><p>A new Internet-of-Things botnet called Kimwolf has spread to more than 2 million devices, forcing infected systems to participate in massive distributed denial-of-service (DDoS) attacks and to relay other malicious and abusive Internet traffic. Kimwolf’s ability to scan the local networks of compromised systems for other IoT devices to infect makes it a sobering threat to organizations, and new research reveals Kimwolf is surprisingly prevalent in government and corporate networks.</p><p><a href="https://krebsonsecurity.com/2026/01/kimwolf-botnet-lurking-in-corporate-govt-networks/" rel="nofollow" class="ellipsis" title="krebsonsecurity.com/2026/01/kimwolf-botnet-lurking-in-corporate-govt-networks/"><span class="invisible">https://</span><span class="ellipsis">krebsonsecurity.com/2026/01/ki</span><span class="invisible">mwolf-botnet-lurking-in-corporate-govt-networks/</span></a></p><p><a href="/tags/botnet/" rel="tag">#botnet</a> <a href="/tags/infosec/" rel="tag">#infosec</a> <a href="/tags/iot/" rel="tag">#IoT</a> <a href="/tags/ddos/" rel="tag">#DDoS</a> <a href="/tags/threatresearch/" rel="tag">#threatresearch</a> <a href="/tags/malware/" rel="tag">#malware</a></p>
Edited 75d ago
<p>New blog post!<br>This is the longest one in quite a while.</p><p>Last year, I held a presentation about the basics of Active Directory pentesting, focusing on "quick wins", easy to exploit vulnerabilities with huge impact.<br>I turned that presentation into a blog post.</p><p>The result is a surface-level overview of some of the most severe Active Directory vulnerabilities.</p><p>I hope it can be useful for aspiring pentesters and Active Directory admins alike.</p><p><a href="https://ti-kallisti.com/general/ms/ad-basics.html" rel="nofollow" class="ellipsis" title="ti-kallisti.com/general/ms/ad-basics.html"><span class="invisible">https://</span><span class="ellipsis">ti-kallisti.com/general/ms/ad-</span><span class="invisible">basics.html</span></a></p><p><a href="/tags/redteam/" rel="tag">#redteam</a> <a href="/tags/pentesting/" rel="tag">#pentesting</a> <a href="/tags/infosec/" rel="tag">#infosec</a> <a href="/tags/activedirectory/" rel="tag">#ActiveDirectory</a> <a href="/tags/sysadmin/" rel="tag">#sysadmin</a> <a href="/tags/microsoft/" rel="tag">#Microsoft</a> <a href="/tags/windows/" rel="tag">#Windows</a></p>
Edited 70d ago
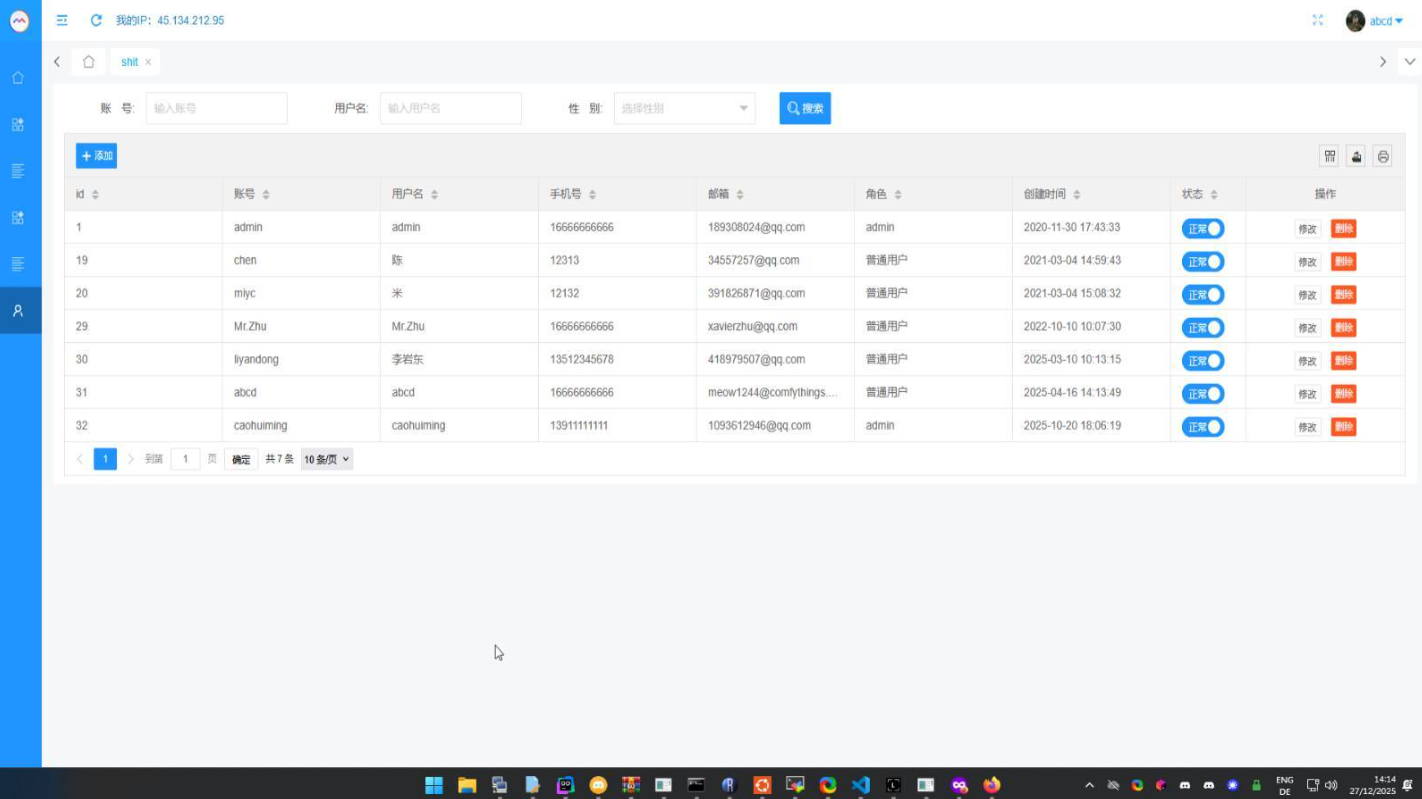
<p>New, from me: Who Operates the Badbox 2.0 Botnet?</p><p>The cybercriminals in control of Kimwolf -- a disruptive botnet that has infected more than 2 million devices -- recently shared a screenshot indicating they'd compromised the control panel for Badbox 2.0, a vast China-based botnet powered by malicious software that comes pre-installed on many Android TV streaming boxes. Both the FBI and Google say they are hunting for the people behind Badbox 2.0, and thanks to bragging by the Kimwolf botmasters we may now have a much clearer idea about that.</p><p><a href="https://krebsonsecurity.com/2026/01/who-operates-the-badbox-2-0-botnet/" rel="nofollow" class="ellipsis" title="krebsonsecurity.com/2026/01/who-operates-the-badbox-2-0-botnet/"><span class="invisible">https://</span><span class="ellipsis">krebsonsecurity.com/2026/01/wh</span><span class="invisible">o-operates-the-badbox-2-0-botnet/</span></a></p><p><a href="/tags/infosec/" rel="tag">#infosec</a> <a href="/tags/botnet/" rel="tag">#botnet</a> <a href="/tags/iot/" rel="tag">#IoT</a> <a href="/tags/android/" rel="tag">#Android</a> <a href="/tags/google/" rel="tag">#Google</a> <a href="/tags/threatresearch/" rel="tag">#threatresearch</a></p>
Edited 70d ago
<p>Motorola announces a partnership with GrapheneOS Foundation<br><a href="https://motorolanews.com/motorola-three-new-b2b-solutions-at-mwc-2026/" rel="nofollow" class="ellipsis" title="motorolanews.com/motorola-three-new-b2b-solutions-at-mwc-2026/"><span class="invisible">https://</span><span class="ellipsis">motorolanews.com/motorola-thre</span><span class="invisible">e-new-b2b-solutions-at-mwc-2026/</span></a></p><p>> Motorola and the GrapheneOS Foundation will work to strengthen smartphone security and collaborate on future devices engineered with GrapheneOS compatibility.</p><p>This could be a gamechanger. Congratulations to <span class="h-card"><a href="https://grapheneos.social/@GrapheneOS" class="u-url mention" rel="nofollow noopener noreferrer" target="_blank">@<span>GrapheneOS</span></a></span>, fingers crossed this works out well!</p><p><a href="/tags/infosec/" rel="tag">#InfoSec</a> <a href="/tags/grapheneos/" rel="tag">#GrapheneOS</a></p>
<p>New blog post!</p><p>Yes, I called it "Cyber Kill Chain".<br>No, I won't apologize.</p><p><a href="https://ti-kallisti.com/tales/cyber-kill-chain.html" rel="nofollow" class="ellipsis" title="ti-kallisti.com/tales/cyber-kill-chain.html"><span class="invisible">https://</span><span class="ellipsis">ti-kallisti.com/tales/cyber-ki</span><span class="invisible">ll-chain.html</span></a></p><p><a href="/tags/infosec/" rel="tag">#infosec</a> <a href="/tags/pentesting/" rel="tag">#pentesting</a> <a href="/tags/redteam/" rel="tag">#redteam</a> <a href="/tags/activedirectory/" rel="tag">#activedirectory</a> <a href="/tags/cyberkillchain/" rel="tag">#cyberkillchain</a></p>
I feel like there's a population of crypto and crypto-adjacent tech people who legitimately don't understand why a long, hard-to-guess string that is stored and shared in cleartext is very different from a password and cannot be substituted for one. I feel like a bunch of these folks don't understand why.<br><br>I'm not going to name and shame but I'm in the midst of a conversation on this, which is why it's top of mind.<br><br><a href="/tags/tech/" rel="tag">#tech</a> <a href="/tags/dev/" rel="tag">#dev</a> <a href="/tags/crypto/" rel="tag">#crypto</a> <a href="/tags/security/" rel="tag">#security</a> <a href="/tags/cybersecurity/" rel="tag">#cybersecurity</a> <a href="/tags/infosec/" rel="tag">#InfoSec</a><br>
<p>We are honoured to be one of the first recipients of the Nominet DNS Fund, which recognises the importance of supporting the quiet work behind the scenes. </p><p>We thank <span class="h-card"><a href="https://mastodon.social/@Nominet" class="u-url mention" rel="nofollow noopener noreferrer" target="_blank">@<span>Nominet</span></a></span> for their forward thinking - helping public interest nonprofits, such as Quad9, who work every day to maintain internet integrity, and the security and privacy of end users around the world.</p><p><a href="https://quad9.net/news/press/nominet-invests-in-quad9/" rel="nofollow" class="ellipsis" title="quad9.net/news/press/nominet-invests-in-quad9/"><span class="invisible">https://</span><span class="ellipsis">quad9.net/news/press/nominet-i</span><span class="invisible">nvests-in-quad9/</span></a></p><p>Congratulations to the other recipients!</p><p><a href="/tags/dns/" rel="tag">#DNS</a> <a href="/tags/internetintegrity/" rel="tag">#internetintegrity</a> <a href="/tags/privacy/" rel="tag">#privacy</a> <a href="/tags/infosec/" rel="tag">#infosec</a></p>
<p>Watching the livestream of the Artemis II launch, I just witnessed one of the astronauts type in the password on their tablet while sitting in the capsule on camera.</p><p><a href="/tags/artemisii/" rel="tag">#ArtemisII</a> <a href="/tags/artemis/" rel="tag">#Artemis</a> <a href="/tags/artemis2/" rel="tag">#Artemis2</a> <a href="/tags/nasa/" rel="tag">#NASA</a> <a href="/tags/infosec/" rel="tag">#InfoSec</a> <a href="/tags/cybersecurity/" rel="tag">#cybersecurity</a> <a href="/tags/opsec/" rel="tag">#OpSec</a> <a href="/tags/privacy/" rel="tag">#Privacy</a> <a href="/tags/spaceexploration/" rel="tag">#SpaceExploration</a></p>
Edited 4d ago
<p>There used to be a time when building out a botnet required *some* work – writing exploits, taking over devices, obscuring the purpose of the executable, etc.</p><p>Not any more!</p><p>Instead of "malware", call it an "AI agent" and people will just happily install it on their devices with full root privileges!<br><a href="https://github.com/jgamblin/OpenClawCVEs/" rel="nofollow" class="ellipsis" title="github.com/jgamblin/OpenClawCVEs/"><span class="invisible">https://</span><span class="ellipsis">github.com/jgamblin/OpenClawCV</span><span class="invisible">Es/</span></a></p><p>Bam! RCE by asking nicely.</p><p>🧵</p><p><a href="/tags/openclaw/" rel="tag">#OpenClaw</a> <a href="/tags/ai/" rel="tag">#AI</a> <a href="/tags/hype/" rel="tag">#Hype</a> <a href="/tags/infosec/" rel="tag">#InfoSec</a></p>
Edited 2d ago
<p>As someone in infosec, how do you handle your personal email? <br> <br> I got tired of Gmail reading everything, so I built a self-hosted <br> alternative with: <br> - X25519 + AES-256-GCM encryption <br> - Postfix/Dovecot on a French VPS <br> - SPF/DKIM/DMARC + fail2ban <br> - An AI cockpit that classifies urgent vs noise <br> <br> Curious what setups other infosec people use. ProtonMail? <br> Self-hosted? Something else? <br> <br> <a href="/tags/infosec/" rel="tag">#infosec</a> <a href="/tags/email/" rel="tag">#email</a> <a href="/tags/privacy/" rel="tag">#privacy</a> <a href="/tags/selfhosted/" rel="tag">#selfhosted</a> <a href="/tags/encryption/" rel="tag">#encryption</a></p>
<p>A Meta exec threatened to fire anyone who put OpenClaw on a work laptop. That's not being paranoid either. OpenClaw just patched a flaw that allowed anyone with the lowest permission level to silently escalate to full admin. No user interaction. No second exploit needed. Just pairing access, and you own the instance. On top of that, 63% of the 135,000 internet-exposed OpenClaw instances were running with zero authentication. On those deployments, the "lowest permission" wasn't even required. Any network visitor could just walk in. 😳 </p><p>🧩 The patches dropped Sunday. The CVE listing didn't come until Tuesday. Attackers had a two-day head start.</p><p>🔑 Full admin means read all connected data sources, exfiltrate stored credentials, execute arbitrary tool calls, and pivot to whatever else the agent touches. Slack. Discord. Files. Logged-in sessions. All of it.</p><p>🤔 The real question isn't whether OpenClaw has security problems. Every tool does. The question is whether your organization decided to hand an inherently unpredictable LLM the keys to your environment before asking who else might be able to grab them.</p><p>If you're running OpenClaw, check your pairing approval logs. Then have an honest conversation about whether the productivity trade-off still makes sense.</p><p><a href="https://arstechnica.com/security/2026/04/heres-why-its-prudent-for-openclaw-users-to-assume-compromise/" rel="nofollow" class="ellipsis" title="arstechnica.com/security/2026/04/heres-why-its-prudent-for-openclaw-users-to-assume-compromise/"><span class="invisible">https://</span><span class="ellipsis">arstechnica.com/security/2026/</span><span class="invisible">04/heres-why-its-prudent-for-openclaw-users-to-assume-compromise/</span></a><br><a href="/tags/cybersecurity/" rel="tag">#Cybersecurity</a> <a href="/tags/aiagents/" rel="tag">#AIAgents</a> <a href="/tags/zerotrust/" rel="tag">#ZeroTrust</a> <a href="/tags/security/" rel="tag">#security</a> <a href="/tags/privacy/" rel="tag">#privacy</a> <a href="/tags/cloud/" rel="tag">#cloud</a> <a href="/tags/infosec/" rel="tag">#infosec</a></p>