<p><a href="/tags/security/" rel="tag">#security</a></p><p>Forwarded from bupt.moe<br><a href="https://t.me/bupt_moe/2647" rel="nofollow"><span class="invisible">https://</span>t.me/bupt_moe/2647</a></p>
security
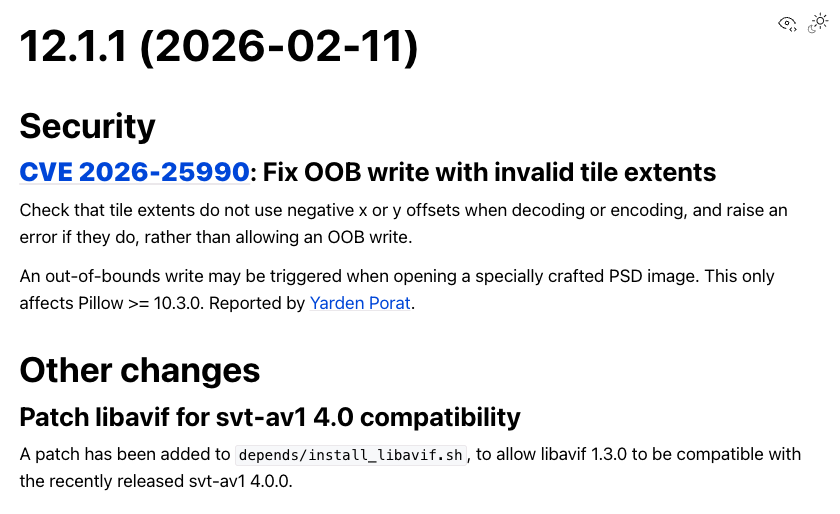
<p>Pillow 12.1.1 has been released!</p><p>This is a security release, addressing an issue in Pillow >= 10.3.0, so upgrade soon!<br><a href="https://pillow.readthedocs.io/en/stable/releasenotes/12.1.1.html" rel="nofollow" class="ellipsis" title="pillow.readthedocs.io/en/stable/releasenotes/12.1.1.html"><span class="invisible">https://</span><span class="ellipsis">pillow.readthedocs.io/en/stabl</span><span class="invisible">e/releasenotes/12.1.1.html</span></a><br><a href="/tags/python/" rel="tag">#Python</a> <a href="/tags/pillow/" rel="tag">#Pillow</a> <a href="/tags/pythonpillow/" rel="tag">#PythonPillow</a> <a href="/tags/release/" rel="tag">#release</a> <a href="/tags/security/" rel="tag">#security</a></p>
Edited 54d ago
dwm 6.8 dropped on Jan 30 and this one deserves attention.<br><br>Less than a month after 6.7, suckless pushed a security fix and bumped<br>the version. That's pretty rare for dwm.<br><br>If you noticed Telegram's image previews shaking in 6.7, that's why<br>a wrong return value check broke atom property reading entirely.<br><br>Patch: <a href="https://git.suckless.org/dwm/commit/a9aa0d8ffbb548b0b1f9f755557aef2482c0f820.html" rel="nofollow" class="ellipsis" title="git.suckless.org/dwm/commit/a9aa0d8ffbb548b0b1f9f755557aef2482c0f820.html"><span class="invisible">https://</span><span class="ellipsis">git.suckless.org/dwm/commit/a9</span><span class="invisible">aa0d8ffbb548b0b1f9f755557aef2482c0f820.html</span></a><br><br>Six lines changed.<br>Update your build.<br><br><a href="/tags/dwm/" rel="tag">#dwm</a> <a href="/tags/suckless/" rel="tag">#suckless</a> <a href="/tags/security/" rel="tag">#security</a> <a href="/tags/linux/" rel="tag">#linux</a><br>
Edited 53d ago
<p>[$] California's Digital Age Assurance Act and Linux distributions</p><p>A recently enacted law in California imposes an age-verification requirement on operating-system providers beginning next year. The language of the Digital Age Assurance Act does n [...]</p><p><a href="https://lwn.net/Articles/1062112/" rel="nofollow"><span class="invisible">https://</span>lwn.net/Articles/1062112/</a> <a href="/tags/lwn/" rel="tag">#LWN</a> <a href="/tags/linux/" rel="tag">#Linux</a> <a href="/tags/security/" rel="tag">#security</a> <a href="/tags/debian/" rel="tag">#Debian</a></p>
I feel like there's a population of crypto and crypto-adjacent tech people who legitimately don't understand why a long, hard-to-guess string that is stored and shared in cleartext is very different from a password and cannot be substituted for one. I feel like a bunch of these folks don't understand why.<br><br>I'm not going to name and shame but I'm in the midst of a conversation on this, which is why it's top of mind.<br><br><a href="/tags/tech/" rel="tag">#tech</a> <a href="/tags/dev/" rel="tag">#dev</a> <a href="/tags/crypto/" rel="tag">#crypto</a> <a href="/tags/security/" rel="tag">#security</a> <a href="/tags/cybersecurity/" rel="tag">#cybersecurity</a> <a href="/tags/infosec/" rel="tag">#InfoSec</a><br>
<p>My previous bio:<br>From <a href="/tags/northshore/" rel="tag">#northshore</a> Massachusetts relocated to northeastern <a href="/tags/vermont/" rel="tag">#Vermont</a> and not just an aggregation of hashtags but: <a href="/tags/antifascismisproper/" rel="tag">#antifascismIsProper</a> <a href="/tags/vegetarian/" rel="tag">#vegetarian</a> <a href="/tags/ubi/" rel="tag">#UBI</a> <a href="/tags/punk/" rel="tag">#punk</a> <a href="/tags/punchanazi/" rel="tag">#punchanazi</a> <a href="/tags/antitrust/" rel="tag">#antitrust</a> <a href="/tags/records/" rel="tag">#records</a> <a href="/tags/nek/" rel="tag">#NEK</a> <a href="/tags/climate/" rel="tag">#climate</a> <a href="/tags/spiritualjazz/" rel="tag">#spiritualjazz</a> <a href="/tags/decolonization/" rel="tag">#decolonization</a> <a href="/tags/movies/" rel="tag">#movies</a> <a href="/tags/scotusexpansion/" rel="tag">#SCOTUSexpansion</a> <a href="/tags/atheist/" rel="tag">#atheist</a> <a href="/tags/rescue/" rel="tag">#rescue</a> <a href="/tags/dogs/" rel="tag">#dogs</a> <a href="/tags/art/" rel="tag">#art</a> <a href="/tags/antifascism/" rel="tag">#antifascism</a> <a href="/tags/photography/" rel="tag">#photography</a> <a href="/tags/audio/" rel="tag">#audio</a> <a href="/tags/privacy/" rel="tag">#privacy</a> <a href="/tags/bread/" rel="tag">#bread</a> <a href="/tags/puppets/" rel="tag">#puppets</a> <a href="/tags/p2p/" rel="tag">#p2p</a> <a href="/tags/security/" rel="tag">#security</a> <a href="/tags/transparency/" rel="tag">#transparency</a> <a href="/tags/accountability/" rel="tag">#accountability</a> <a href="/tags/intersectionalism/" rel="tag">#intersectionalism</a> <a href="/tags/sober/" rel="tag">#sober</a> <a href="/tags/farmsanctuary/" rel="tag">#farmSanctuary</a> <a href="/tags/resistzionism/" rel="tag">#resistZionism</a><br>I tend to mute or remove followers with neither posts nor bio, and those containing financial-support or revenue-promotion links</p>
<p>A Meta exec threatened to fire anyone who put OpenClaw on a work laptop. That's not being paranoid either. OpenClaw just patched a flaw that allowed anyone with the lowest permission level to silently escalate to full admin. No user interaction. No second exploit needed. Just pairing access, and you own the instance. On top of that, 63% of the 135,000 internet-exposed OpenClaw instances were running with zero authentication. On those deployments, the "lowest permission" wasn't even required. Any network visitor could just walk in. 😳 </p><p>🧩 The patches dropped Sunday. The CVE listing didn't come until Tuesday. Attackers had a two-day head start.</p><p>🔑 Full admin means read all connected data sources, exfiltrate stored credentials, execute arbitrary tool calls, and pivot to whatever else the agent touches. Slack. Discord. Files. Logged-in sessions. All of it.</p><p>🤔 The real question isn't whether OpenClaw has security problems. Every tool does. The question is whether your organization decided to hand an inherently unpredictable LLM the keys to your environment before asking who else might be able to grab them.</p><p>If you're running OpenClaw, check your pairing approval logs. Then have an honest conversation about whether the productivity trade-off still makes sense.</p><p><a href="https://arstechnica.com/security/2026/04/heres-why-its-prudent-for-openclaw-users-to-assume-compromise/" rel="nofollow" class="ellipsis" title="arstechnica.com/security/2026/04/heres-why-its-prudent-for-openclaw-users-to-assume-compromise/"><span class="invisible">https://</span><span class="ellipsis">arstechnica.com/security/2026/</span><span class="invisible">04/heres-why-its-prudent-for-openclaw-users-to-assume-compromise/</span></a><br><a href="/tags/cybersecurity/" rel="tag">#Cybersecurity</a> <a href="/tags/aiagents/" rel="tag">#AIAgents</a> <a href="/tags/zerotrust/" rel="tag">#ZeroTrust</a> <a href="/tags/security/" rel="tag">#security</a> <a href="/tags/privacy/" rel="tag">#privacy</a> <a href="/tags/cloud/" rel="tag">#cloud</a> <a href="/tags/infosec/" rel="tag">#infosec</a></p>